By MyCena | Posted on: 16 April 2026
Critical Infrastructure
By MyCena | Posted on: 16 April 2026
BPO & Contact Centre

By MyCena | Posted on: 12 June 2025
Why Third-Party Access Is The Weakest Link in Enterprise Security
Last month, two major brands Marks & Spencer (M&S) and Coinbase—became
the latest victims in a rising
wave of cyberattacks against third-party helpdesk. These weren’t sophisticated zero-day exploits or state-sponsored
hacks. They were inside jobs, made possible by human-managed credentials in the hands of third
parties.
The fallout? Hundreds of millions in damages, disrupted operations, and shaken customer trust. Here's a
breakdown of what went wrong, why it happened, and how MyCena makes this kind of breach
impossible.
What Happened?
Marks & Spencer (M&S)
Hackers infiltrated M&S by exploiting a third-party contractor with access to their
systems. Once inside, they stole personal customer data including contact details and order histories—and disrupted
online operations. While financial data wasn’t accessed, the impact was still massive: halted online orders, lost
revenue, legal fallout, and shaken customer trust.
- Estimated losses: £43 million per week in halted sales
- Market value impact: Over £1.2 billion wiped out
- Reputational cost: Rising customer complaints and a class-action lawsuit in progress
Coinbase
In Coinbase’s case, attackers bribed overseas customer support contractors to misuse
their internal
access. This allowed them to extract personal information on customers—names, IDs, masked bank details, and more.
Even though login credentials and funds remained untouched, the breach triggered legal action, an extortion attempt,
and hundreds of millions in projected losses.
- Ransom demand: $20 million
- Projected remediation costs: Between $180 million and $400 million
- Legal impact: Ongoing DOJ investigation + civil suits over failure to protect user data
Why It Happened
Despite their size and resources, both organizations relied on third parties to access critical systems
using traditional identity-based methods—typically usernames and passwords or shared credentials.
That’s the
problem.
Traditional credential models are inherently flawed.
When credentials are managed by people—whether internal staff or external contractors—they can be phished, shared,
reused, sold, or stolen. In both breaches, the attackers didn’t need to break in. They just found someone who
already had a key—or made a copy of one.
This is the danger of third-party access in today’s connected supply chains: you inherit every
weakness your vendors and partners have.
Here’s how MyCena makes third-party breaches impossible:
At MyCena , we’ve eliminated the problem at the root: we remove humans from
credential management
entirely.
Here’s how MyCena’s Multi-Layer Dynamic Access Encryption Security
(ML-DAES) prevents
third-party
credential breaches:
- Unphishable Credentials: MyCena generates and encrypts credentials
automatically—users
never see, create, or
share passwords. That means nothing to phish, bribe, or mishandle.
- Access Segmentation: Third-party access is strictly limited by system and
role, and each user
only gets access
to the specific system they need, preventing attackers from moving laterally.
- No Visibility = No Theft: Without credentials being visible, they can’t be phished,
reused, or
sold—even under
coercion or bribery.
- Audit-Ready Logs: Every access action is tracked in real time, ensuring full governance and
instant
audit-readiness across internal and external users.
With MyCena , there’s no password reset to steal, no spreadsheet to leak, and no third-party
weak link to
exploit. Our technology removes the human risk factor by eliminating employee-managed credentials entirely, and
third-party access doesn’t mean third-party risk.
Final Thought
The M&S and Coinbase breaches are wake-up calls for every business that shares access with partners,
vendors, or contractors. You might trust them but can you trust their cybersecurity practices?
Ask yourself: Would you let vendors make physical copies of your office keys and hand them to unknown
staff? That’s exactly what happens when you let humans manage digital credentials.
MyCena makes that scenario obsolete. With encrypted, automated, segmented
access,
you stay in
control—even when access is shared.
Because when no one sees the keys, no one can steal them.
Ready to make phishing a thing of the past?
Book a demo with MyCena today and discover how encrypted, employee-free credential
management can
transform your cybersecurity posture.
By MyCena | Posted on: 4 June 2025
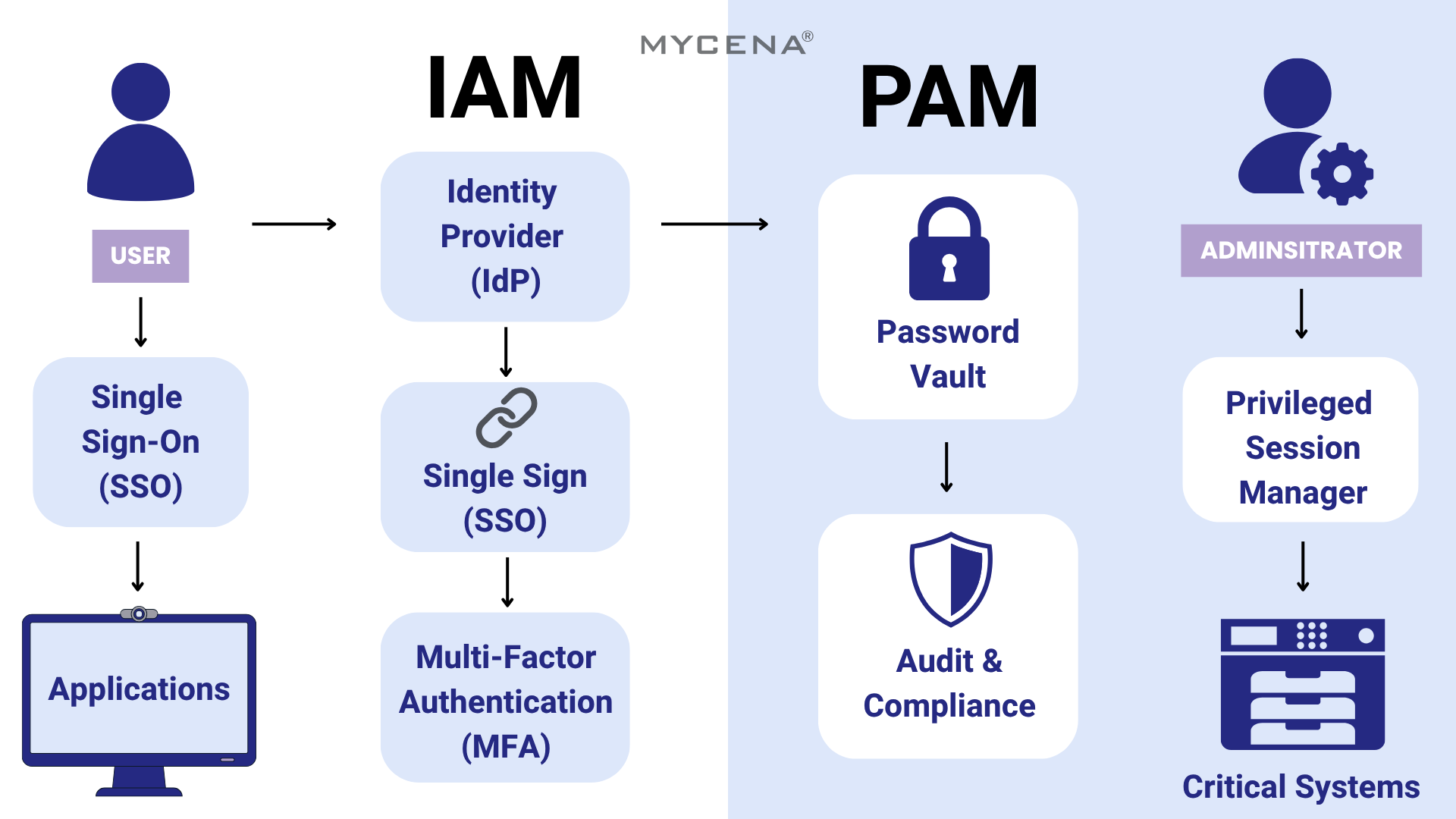
IAM vs. PAM: Why Understanding the Difference is Key to Your Cybersecurity Strategy
In today's digital landscape, managing access isn't just an IT task—it's a critical line of defense. Two
terms often thrown around in the cybersecurity world are IAM (Identity Access Management) and PAM
(Privileged Access Management) . They sound similar, and they are related—but mixing them up could
leave your systems exposed in ways you didn't expect.
Let's break them down and explain how each plays a unique (and essential) role in keeping your
organization secure.
What is IAM?
Identity and Access Management (IAM) is the foundational layer of digital access
control. It's like the
front desk of
your digital office—checking who each person is and what they're allowed to do.
IAM ensures that every user , whether it's an employee, customer, contractor, or
partner, has the right
level of
access to the right resources —nothing more, nothing less.
IAM systems handle:
- Creating and managing user identities across systems
- Controlling logins with secure methods like Single Sign-On (SSO), multi-factor authentication (MFA), or
biometrics
- Automating onboarding and offboarding processes
- Assigning access based on roles (RBAC)
- Tracking who accessed what and when (audit trails)
Popular IAM tools: Okta, Microsoft Entra ID (formerly Azure AD), Auth0
Think of IAM as the digital ID badge and access gate for everyone in your ecosystem.
What is PAM?
While IAM is about everyone , Privileged Access Management (PAM) is about the few — the
users who hold
the digital master keys.
PAM is a specialized subset of IAM focused on securing privileged accounts , such as
system
administrators, DevOps engineers, and IT staff. These accounts can access your most critical infrastructure, and if
compromised, they can cause catastrophic damage.
PAM solutions are designed to:
- Store and manage powerful credentials in secure password vaults
- Monitor and record sessions of users with elevated privileges
- Enforce Just-In-Time (JIT) access (temporary, on-demand permissions)
- Detect unusual or risky behavior through user behavior analytics
- Enforce Segregation of Duties (SoD) to prevent conflicts of interest
Popular PAM tools: CyberArk, BeyondTrust, Delinea (formerly Thycotic)
Where IAM manages the front door for everyone, PAM secures the keys to the server room.
IAM vs. PAM: Quick Comparison
| Feature |
IAM |
PAM |
| Who it covers |
All users (staff, partners, customers) |
Privileged users (admins, IT, DevOps) |
| Main goal |
Manage user identities and general access |
Protect and monitor high-risk access |
| Focus |
Authentication & role-based access |
Secure credential vaulting & session control |
| Use case |
Needed by all organizations |
Critical for sensitive or regulated systems |
Why You Need Both
Relying on IAM without PAM is like having a well-guarded office lobby but no lock on the server room.
Conversely, using PAM without IAM would be like locking up the IT admin while leaving the rest of the building open.
For a robust access security strategy, you need both IAM and PAM working together :
- IAM ensures everyone is verified and appropriately authorized.
- PAM ensures only the right people , at the right time, can touch your most sensitive systems—with oversight and
control.
Final Thoughts
As cyber threats grow more advanced—especially with phishing, insider risks, and AI-driven
attacks—relying solely on traditional identity or access tools leaves gaps. IAM and PAM are
essential pieces of the
security puzzle, but they still depend on one vulnerable element: human-managed credentials.
That's where MyCena comes in.
MyCena takes IAM and PAM a step further by removing the weakest link in the chain,
passwords. With
encrypted, automated credential management, MyCena ensures employees never create, see, or share
credentials. That
makes phishing irrelevant, access segmented, and compliance a breeze.
By complementing your IAM and PAM strategies, MyCena helps eliminate credential-based
attacks entirely
, simplifying governance while boosting your organization's resilience and efficiency.
No passwords. No phishing. No problem.
MyCena. Security done for you.

By MyCena | Posted on: 15 April 2024
Microsoft left internal passwords exposed in latest security blunder
With no password protection, a Microsoft server containing a variety of security credentials used by Microsoft employees to access internal systems was accessible by anyone on the internet.
Access is the biggest weakness in cybersecurity. Companies need to control their credentials and encrypt them so they can't be known and disclosed.

By MyCena | Posted on: 19 February 2024
Hackers ‘steal your face’ to create deepfakes that rob bank accounts
With no way to validate identity from users' biometric, financial systems are massively exposed to identity theft fraud.
=> Biometric authentication are handy PIN code replacement but not more secure. Why? Because your fingerprints, your face, and your voice are not secrets.
=> Biometrics are increasingly being scraped, stored, and analyzed by threat actors.
=> By exploiting IP cameras' video databases, hackers can gather bits of iris and fingerprint and "with enough repetition, compute power, and time, they can potentially crack a person’s full biometrics."
=> "Biometric data is useful for in-person authentication, and really dangerous for remote authentication". Biometric data are like a complex key. Once transmitted, users aren’t authenticating the actual biometric, they are verifying something that looks a lot like a password.
our financial system is built in a lot of assumed-but-not-verified trust.will continue to be exacerbated by technologies like deep fakes as long as our banking institutions trust transmitted copies of a biometric.”